It started with a simple email.
For years, NASA scientists, Air Force engineers, and university researchers across the United States received messages that appeared to come from trusted colleagues — requests to share software, source code, or technical documents. The emails were polished, specific, and convincing. Many recipients replied without hesitation.
They were writing to a spy.
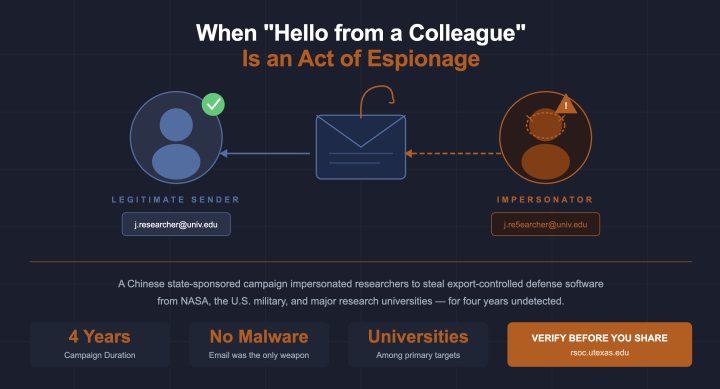
Federal court documents and reporting from The Hacker News revealed the full scope of a multi-year phishing operation orchestrated by Song Wu, an engineer at the Aviation Industry Corporation of China (AVIC) — a Chinese state-owned aerospace and defense conglomerate. From 2017 to 2021, Song Wu and his associates impersonated American researchers — real people with real job titles and email addresses that closely resembled legitimate ones — to trick employees at NASA, the Air Force, the Navy, the Army, the FAA, and multiple major research universities into handing over sensitive, export-controlled defense software.
The software Song Wu obtained wasn't destined for a research paper. It was designed to advance China's military aerospace capabilities — without the years of R&D that American institutions invested to build it. The U.S. Department of Justice charged Song Wu in September 2024, but the campaign's tactics are far from retired.
The Threat Is Closer Than You Think
Texas is home to some of the nation's most active research universities, institutions conducting federally funded work in aerospace, defense, energy, cybersecurity, and emerging technologies. Many of these institutions are RSOC constituents. They hold exactly the kind of intellectual property that sophisticated foreign actors covet.
Spear-phishing, targeted phishing that impersonates specific, known individuals, remains one of the most effective tools in a nation-state attacker's playbook, precisely because it exploits trust. Song Wu didn't crack a firewall or exploit a zero-day vulnerability. He crafted convincing personas and sent emails. His operation sustained itself for four years across multiple federal agencies and universities because **the emails were believable**.
What Made This Campaign So Effective
**Impersonation of real people.** Attackers researched actual American engineers and researchers, then created email addresses that closely matched their real identities — sometimes differing by only a character or two.
**Context-aware targeting.** Before reaching out, attackers learned enough about a target's actual work to make requests feel natural. A message about a specific software tool from someone who appeared to know the project didn't raise red flags.
**Low technical bar, high-value payoff.** No sophisticated malware was deployed. A convincing email was enough. This is what makes the tactic so durable: it requires no technical vulnerability to succeed, only a moment of misplaced trust.
What RSOC Constituents Should Do
This campaign is a prompt for every Texas higher education institution to revisit how researchers and staff handle unsolicited requests for software, data, or technical materials, even from apparent colleagues.
**Verify before you share.** If a colleague emails unexpectedly asking for source code, research data, or documents, confirm the request through a second channel, a phone call, a Teams message, or an in-person conversation, before responding.
**Train researchers, not just IT staff.** Faculty, researchers, and graduate students are frequently targeted because academic culture encourages open sharing of information. Security awareness programs need to reach beyond the IT department and into the labs and offices where sensitive work happens.
**Know your export control obligations.** Ensure your institution has a clear process for identifying which software and research materials are subject to U.S. export control regulations, and that researchers know what requires authorization before sharing with anyone, including apparent colleagues.
**Protect your email perimeter.** DMARC, DKIM, and SPF configurations help reduce the risk of look-alike domain attacks. Consider email security tools that flag messages from domains that closely resemble known organizations.
**Report suspicious requests.** If a researcher or staff member receives an unexpected request for sensitive materials, even from a seemingly familiar sender, encourage them to report it to your institutional security team before responding.
The Bottom Line
The Song Wu case is a reminder that research institutions are not bystanders in the geopolitical competition playing out in cyberspace, they are the target. Universities hold the intellectual property that nation-state actors want, and the culture of openness that makes academic collaboration thrive can also create an opening for exploitation.
The good news: the defenses against spear-phishing are well understood. Awareness, verification habits, and clear reporting channels can significantly reduce risk. The RSOC is here to help your institution build and strengthen those defenses.
Questions about your institution's exposure to spear-phishing threats or interest in security awareness resources? Contact the RSOC team at RSOC@utexas.edu (https://rsoc.utexas.edu).