The Closing Window: AI Is Compressing Your Vulnerability Patch Timeline—And Attackers Are Already Exploiting It
A new inflection point in cybersecurity has arrived: AI systems can now autonomously discover and weaponize software vulnerabilities faster than human teams can respond. Texas higher education institutions need to rethink how they prioritize and act on vulnerability data.
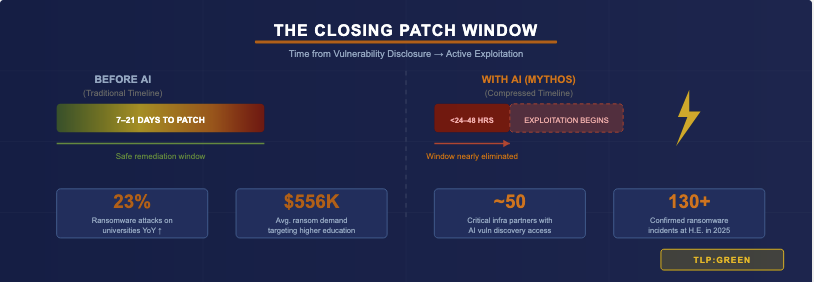
For years, security teams have operated on an unspoken assumption: when a critical vulnerability is disclosed, there are days—sometimes weeks—before threat actors figure out how to reliably exploit it. That window, however uncomfortable, gave patch management programs time to identify affected systems, test remediation, and deploy fixes. That assumption is no longer safe to make.
A Qualys analysis published this week describes what they're calling the "Mythos Inflection Point"—a seismic shift driven by AI systems now capable of autonomously discovering, analyzing, and weaponizing software vulnerabilities at a depth and speed that previously required teams of experienced human researchers. The practical consequence is a coming wave of vulnerability disclosures paired with dramatically compressed timelines to active exploitation.
What Has Changed
Earlier this year, Anthropic released its frontier AI model as part of Project Glasswing with access provisioned to approximately 50 critical infrastructure partners—including Amazon, Microsoft, and Apple—specifically to identify novel software vulnerabilities at scale. The result is a surge in vendor advisories, emergency patches, and CVE disclosures arriving faster than existing vulnerability management pipelines were designed to process.
The threat calculus is straightforward: if defensive AI is discovering vulnerabilities this quickly, offensive actors—nation-states, ransomware groups, and independent researchers—are acquiring or building similar capabilities. The traditional model where defenders could reasonably assume days of quiet after a CVE disclosure is eroding. Security teams that still operate on week-long patching cycles for critical vulnerabilities are operating with assumptions that no longer hold.
⚠ The Core Risk for Texas Institutions
Ransomware attacks against colleges and universities increased 23% year-over-year in 2025, with over 130 confirmed incidents and average ransom demands of $556,000. Many of those attacks began with unpatched vulnerabilities—systems where IT teams simply hadn't yet gotten to the fix. With exploitation windows now measured in hours rather than days, the margin for delay has all but disappeared.
What "Compressed Exploitation" Means in Practice
The shift is not just about speed. AI-assisted vulnerability research changes the character of the threat in several ways relevant to higher education environments:
- More CVEs, faster: Software vendors are now disclosing vulnerabilities at a pace that strains already-thin IT security staffing at many Texas institutions. Prioritization frameworks that were adequate before may no longer keep up.
- Less time between disclosure and weaponization: Proof-of-concept exploit code is appearing within hours of disclosure for high-profile vulnerabilities. The window in which a system is "known vulnerable but not yet actively exploited" is shrinking toward zero.
- Supply chain amplification: AI vulnerability discovery is surfacing flaws in shared dependencies—open-source libraries, plugins, and cloud service connectors—that underpin dozens of university systems simultaneously. A single upstream vulnerability can affect research systems, student portals, and administrative platforms at once.
- Credential and identity attacks remain the primary entry: Even with faster vulnerability exploitation, attackers continue to favor identity-based intrusion chains. Faster exploitation of auth-bypass CVEs makes identity hygiene and MFA enforcement more—not less—critical.
Adapting Your Vulnerability Program for This Environment
The Qualys analysis makes clear that the hardest part of vulnerability management was never finding vulnerabilities—it was determining which findings represent real, exploitable risk in a specific environment, with specific mitigating controls in place, against the most critical business services. That determination now needs to happen faster than ever.
- Re-evaluate your SLAs. If your current vulnerability management policy sets a 30-day remediation window for "HIGH" severity CVEs on internet-facing systems, that policy is likely no longer fit for purpose. Consider moving to risk-tiered SLAs with 24–72 hour targets for critical, externally exposed systems.
- Prioritize asset exposure context. Not all vulnerabilities are equal. A critical CVE on an internal development server is different from the same CVE on a student-facing authentication portal. Tooling that maps vulnerability severity to asset criticality and network exposure is essential.
- Accelerate your patching pipeline. Identify and remove friction in your patching workflow. Emergency change windows, pre-approved patching procedures for vendor-supported software, and automated deployment tooling all reduce the time between "patch available" and "patch deployed."
- Increase visibility into third-party and supply chain dependencies. Maintain an accurate software bill of materials (SBOM) for critical systems. When a shared library vulnerability is disclosed, you need to know immediately which of your systems are affected.
- Tune detection to compensate. When you cannot patch immediately, compensating controls matter. Network segmentation, exploit mitigations, and enhanced logging on vulnerable systems extend your effective response window.
ℹ RSOC Resources
UT RSOC member institutions have access to the RSOC vulnerability intelligence feed, which correlates CVE disclosures with in-the-wild exploitation evidence and provides Texas higher education context. Contact the RSOC team at rsoc@utexas.edu to ensure your institution is receiving these feeds and to discuss Isora GRC integration for continuous vulnerability tracking.