Friend Request From Pyongyang: How North Korean Hackers Are Targeting University Communities
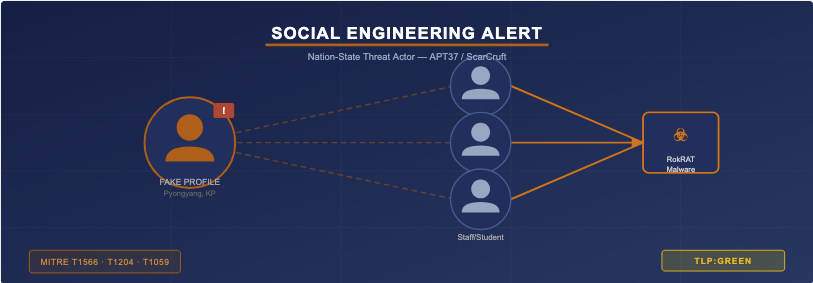
APT37—North Korea's state-sponsored cyber unit—is sending fake Facebook friend requests to researchers, faculty, and academic professionals as the opening move in a multi-stage malware campaign. Here's what the UT RSOC community needs to know.
A freshly attributed campaign from North Korean threat actor APT37 (also known as ScarCruft or Group123) is using some of the most ordinary digital touchpoints in academic life—social media friend requests—as the entry point for sophisticated cyberespionage. The campaign, analyzed this week by security researchers and flagged in threat intelligence feeds shared with the UT RSOC team, is specifically designed to exploit the professional networking habits of researchers, policy analysts, and academic staff.
Unlike the phishing emails that most security trainings warn about, this campaign starts with an apparently routine Facebook friend request—and by the time a malicious payload arrives, the target has often been engaged in conversation for days or even weeks.
How the Attack Unfolds
- 1 Fake Profile — Initial Contact Attackers create Facebook accounts with locations set to North Korean cities (Pyongyang, Pyongsong). They send friend requests to academics, government-adjacent researchers, and defense-policy professionals. The accounts appear plausible at a glance.
- 2 Trust-Building via Messenger & Telegram Once accepted, conversation moves to Messenger and eventually Telegram. Attackers use pretexting—posing as colleagues, journalists, or think-tank contacts—and discuss topics relevant to the target's research area to build credibility over time.
- 3 Trojanized Software Delivery The target is sent a ZIP archive containing a tampered version of Wondershare PDFelement along with PDF documents, with instructions to install the software to open "encrypted research files." The installer appears legitimate.
- 4 RokRAT Malware Deployment Launching the installer triggers embedded shellcode that connects to a compromised C2 server and retrieves a second-stage payload disguised as a JPG image—a tactic designed to evade endpoint detection tools. The final payload is RokRAT.
5 Silent Exfiltration RokRAT abuses Zoho WorkDrive as its command-and-control channel—a legitimate cloud service that rarely triggers enterprise network alerts. The malware captures screenshots, runs system commands, harvests credentials, and exfiltrates research data.
Why the Texas Higher Education Community Is at Risk
APT37 has a documented history of targeting academics, policy researchers, journalists, and human rights advocates—particularly those working on topics of strategic interest to Pyongyang, including Korean Peninsula security, nuclear nonproliferation, sanctions, and defense technology. Texas institutions host world-class research programs in many of these areas, and their students and faculty represent exactly the profile APT37 seeks.
The use of everyday platforms like Facebook removes the technical barrier to compromise. A researcher doesn't need to click a malicious email link or visit a spoofed website—just accepting a friend request and later downloading what appears to be a productivity tool is sufficient. This is particularly concerning in academic environments where open collaboration and cross-institutional networking are the norm.
Indicators of Compromise
| Type | Indicator | Note |
|---|---|---|
| Facebook Account | richardmichael0828 | Known attacker persona; location: Pyongyang |
| Facebook Account | johnsophia0414 | Known attacker persona; location: Pyongsong |
| C2 Domain | japanroom[.]com | Compromised site used for stage-2 payload delivery |
| Payload File | 1288247428101.jpg | RokRAT disguised as JPG; dropped from C2 |
| Trojanized Installer | Wondershare PDFelement | Legitimate software tampered with malicious shellcode |
| C2 Channel | Zoho WorkDrive (legitimate) | Abused as covert command channel by RokRAT |
Recommended Actions for RSOC Constituents
- Brief faculty, researchers, and graduate students on this campaign. Academic communities are the primary target—awareness is the most effective control.
- Remind staff and students to verify the identity of any new social media contacts before engaging, especially those expressing interest in ongoing research or requesting document exchanges.
- Instruct users to never install software received through social messaging platforms, regardless of how legitimate it appears.
- Add
japanroom[.]comto DNS blocklists and review proxy/firewall logs for any outbound connections to this domain. - Monitor endpoint telemetry for PDF-related application installs outside of approved software channels (Wondershare PDFelement as a delivery vector).
- Review cloud storage integrations—particularly Zoho WorkDrive—for any anomalous API activity or unexpected connections from endpoints.